Client-Side Encryption
Encrypt sensitive payment information on the client side to reduce your PCI compliance scope
Client-side encryption refers to encrypting sensitive data (credit card number, expiration date, and CVV) on the client side device before sending it to your server. This enables you to keep your PCI compliance requirements limited to the SAQ A-EP level.
For implementation instructions for BlueSnap's Payment API and Extended Payment API, go to the Developer Hub.
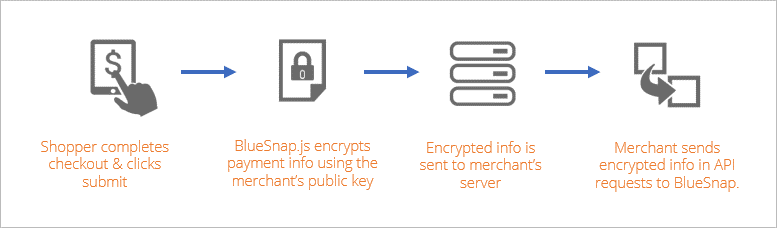
How client-side encryption works
BlueSnap provides an encryption library for each platform: web, iOS, and Android. The encryption library uses your Client-Side Encryption key to encrypt sensitive payment fields like the credit card number and security code.
Encryption is done on the checkout page on the client side device, which means that you don't have to handle sensitive data because it is encrypted before it sent to your server. This makes payments more secure and also reduces your PCI compliance burden.
Once the encrypted data has been sent to your server, you can then pass it on to BlueSnap for transaction processing. BlueSnap will decrypt the data, process the transaction, and then send you information about the status of the transaction.
Updated 4 months ago